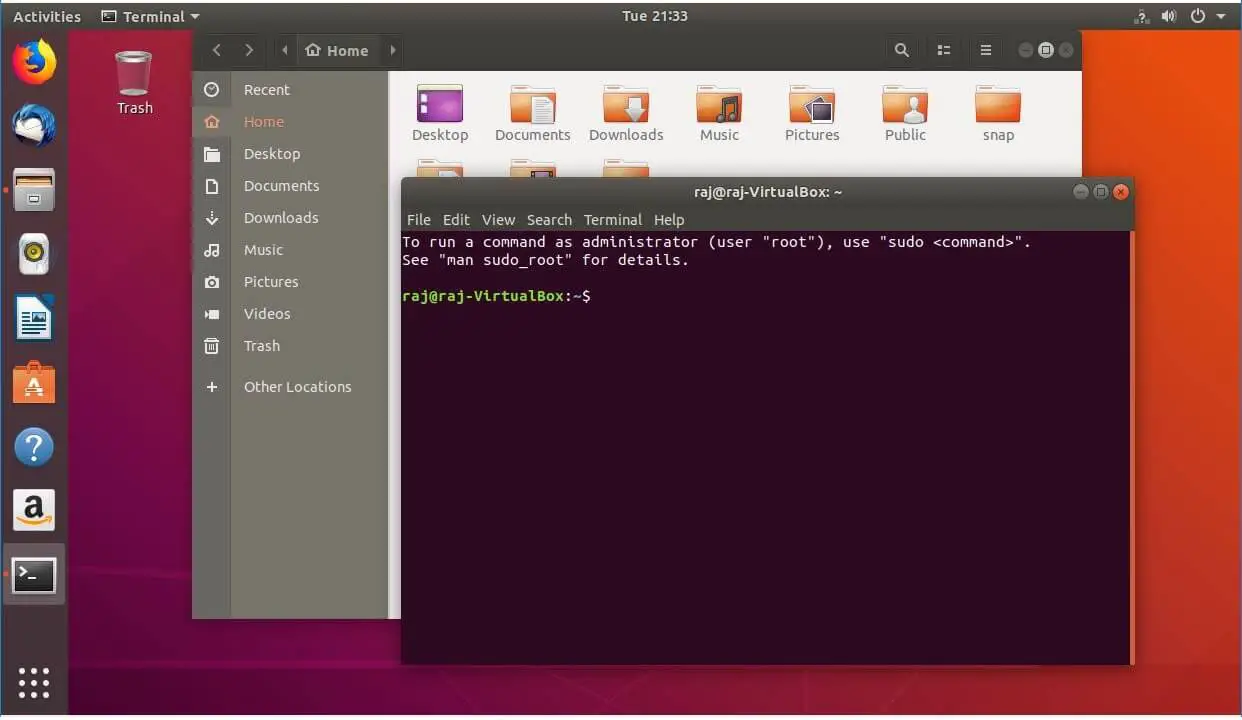
In this tutorial, we'll explain how to set up a static IP address on Ubuntu 18.04. Generally, IP addresses are assigned dynamically by your router DHCP server. Setting a static IP address on your Ubuntu machine may be required in different situations, such as configuring port forwarding or running a media server on your network. This tutorial shows the installation of an Ubuntu 18.04 LTS minimal server in detail with many screenshots. The purpose of the guide is to show the basic installation of Ubuntu 18.04 LTS that can be used as the basis for our other Ubuntu tutorials here at howtoforge like our perfect server guides.
Select an image
Ubuntu is distributed on two types of images described below.
Desktop image
The desktop image allows you to try Ubuntu without changing your computer at all, and at your option to install it permanently later. This type of image is what most people will want to use. You will need at least 1024MiB of RAM to install from this image.
There is one image available:
- 64-bit PC (AMD64) desktop image
- Choose this if you have a computer based on the AMD64 or EM64T architecture (e.g., Athlon64, Opteron, EM64T Xeon, Core 2). Choose this if you are at all unsure.
Server install image
The server install image allows you to install Ubuntu permanently on a computer for use as a server. It will not install a graphical user interface.
There is one image available:
- 64-bit PC (AMD64) server install image
- Choose this if you have a computer based on the AMD64 or EM64T architecture (e.g., Athlon64, Opteron, EM64T Xeon, Core 2). Choose this if you are at all unsure.
If you require LVM, RAID, multipath, network vlans, or network interface bonding during the installation; if you need to reuse existing partitions on your installation disk; or for support for other architectures besides AMD64/EM64T, see the alternative images location.
A full list of available files, including BitTorrent files, can be found below.
If you need help burning these images to disk, see the Image Burning Guide.
| Name | Last modified | Size |
|---|---|---|
| Parent Directory | - | |
| FOOTER.html | 2018-04-26 20:59 | 27 |
| HEADER.html | 2018-04-27 00:54 | 2.3K |
| MD5SUMS | 2020-08-13 15:36 | 3.2K |
| MD5SUMS-metalink | 2018-04-26 21:00 | 144 |
| MD5SUMS-metalink.gpg | 2018-04-26 21:00 | 916 |
| MD5SUMS.gpg | 2020-02-12 14:39 | 916 |
| SHA1SUMS | 2020-08-13 15:37 | 3.5K |
| SHA1SUMS.gpg | 2020-02-12 14:39 | 916 |
| SHA256SUMS | 2020-08-13 15:37 | 4.5K |
| SHA256SUMS.gpg | 2020-02-12 14:39 | 916 |
| source/ | 2019-08-08 12:33 | - |
| ubuntu-18.04-desktop-amd64.iso | 2018-04-26 18:44 | 1.8G |
| ubuntu-18.04-desktop-amd64.iso.torrent | 2018-04-26 20:58 | 72K |
| ubuntu-18.04-desktop-amd64.iso.zsync | 2018-04-26 20:58 | 3.6M |
| ubuntu-18.04-desktop-amd64.list | 2018-04-26 18:44 | 7.9K |
| ubuntu-18.04-desktop-amd64.manifest | 2018-04-26 18:40 | 53K |
| ubuntu-18.04-desktop-amd64.metalink | 2018-04-26 21:00 | 45K |
| ubuntu-18.04-live-server-amd64.iso | 2018-04-26 19:48 | 806M |
| ubuntu-18.04-live-server-amd64.iso.torrent | 2018-04-26 20:59 | 32K |
| ubuntu-18.04-live-server-amd64.iso.zsync | 2018-04-26 20:59 | 1.6M |
| ubuntu-18.04-live-server-amd64.list | 2018-04-26 19:49 | 8.0K |
| ubuntu-18.04-live-server-amd64.metalink | 2018-04-26 21:00 | 47K |
| ubuntu-18.04-preinstalled-server-armhf+raspi2.img.xz | 2018-04-26 19:04 | 296M |
| ubuntu-18.04-preinstalled-server-armhf+raspi2.img.xz.zsync | 2018-04-26 20:57 | 518K |
| ubuntu-18.04-preinstalled-server-armhf+raspi2.manifest | 2018-04-26 19:04 | 13K |
| ubuntu-18.04-server-amd64.iso | 2018-04-26 18:30 | 704M |
| ubuntu-18.04-server-amd64.iso.torrent | 2018-04-26 21:02 | 28K |
| ubuntu-18.04-server-amd64.iso.zsync | 2018-04-26 21:01 | 1.4M |
| ubuntu-18.04-server-amd64.jigdo | 2018-04-26 21:01 | 132K |
| ubuntu-18.04-server-amd64.list | 2018-04-26 18:30 | 96K |
| ubuntu-18.04-server-amd64.metalink | 2018-04-26 21:24 | 1.0K |
| ubuntu-18.04-server-amd64.template | 2018-04-26 18:30 | 130M |
| ubuntu-18.04-server-arm64.iso | 2018-04-26 18:32 | 670M |
| ubuntu-18.04-server-arm64.iso.torrent | 2018-04-26 21:02 | 26K |
| ubuntu-18.04-server-arm64.iso.zsync | 2018-04-26 21:02 | 1.3M |
| ubuntu-18.04-server-arm64.jigdo | 2018-04-26 21:02 | 156K |
| ubuntu-18.04-server-arm64.list | 2018-04-26 18:32 | 89K |
| ubuntu-18.04-server-arm64.metalink | 2018-04-26 21:24 | 1.0K |
| ubuntu-18.04-server-arm64.template | 2018-04-26 18:32 | 78M |
| ubuntu-18.04-server-ppc64el.iso | 2018-04-26 18:33 | 736M |
| ubuntu-18.04-server-ppc64el.iso.torrent | 2018-04-26 21:02 | 29K |
| ubuntu-18.04-server-ppc64el.iso.zsync | 2018-04-26 21:02 | 1.4M |
| ubuntu-18.04-server-ppc64el.jigdo | 2018-04-26 21:02 | 161K |
| ubuntu-18.04-server-ppc64el.list | 2018-04-26 18:33 | 91K |
| ubuntu-18.04-server-ppc64el.metalink | 2018-04-26 21:24 | 1.0K |
| ubuntu-18.04-server-ppc64el.template | 2018-04-26 18:33 | 89M |
| ubuntu-18.04-server-s390x.iso | 2018-04-26 18:34 | 565M |
| ubuntu-18.04-server-s390x.iso.torrent | 2018-04-26 21:02 | 22K |
| ubuntu-18.04-server-s390x.iso.zsync | 2018-04-26 21:02 | 1.1M |
| ubuntu-18.04-server-s390x.jigdo | 2018-04-26 21:02 | 125K |
| ubuntu-18.04-server-s390x.list | 2018-04-26 18:34 | 87K |
| ubuntu-18.04-server-s390x.metalink | 2018-04-26 21:24 | 1.0K |
| ubuntu-18.04-server-s390x.template | 2018-04-26 18:34 | 114M |
| ubuntu-18.04.1-desktop-amd64.iso | 2018-07-25 03:22 | 1.8G |
| ubuntu-18.04.1-desktop-amd64.iso.torrent | 2018-07-26 16:55 | 73K |
| ubuntu-18.04.1-desktop-amd64.iso.zsync | 2018-07-26 16:55 | 3.6M |
| ubuntu-18.04.1-desktop-amd64.list | 2018-07-25 03:22 | 7.7K |
| ubuntu-18.04.1-desktop-amd64.manifest | 2018-07-25 03:19 | 55K |
| ubuntu-18.04.1-desktop-amd64.metalink | 2018-11-29 23:27 | 51K |
| ubuntu-18.04.1-live-server-amd64.iso | 2018-11-29 22:30 | 812M |
| ubuntu-18.04.1-live-server-amd64.iso.torrent | 2018-07-26 16:54 | 32K |
| ubuntu-18.04.1-live-server-amd64.iso.zsync | 2018-07-26 16:54 | 1.6M |
| ubuntu-18.04.1-live-server-amd64.list | 2018-07-25 23:39 | 7.8K |
| ubuntu-18.04.1-live-server-amd64.manifest | 2018-07-25 23:29 | 14K |
| ubuntu-18.04.1-live-server-amd64.metalink | 2018-11-29 23:01 | 55K |
| ubuntu-18.04.1-preinstalled-server-armhf+raspi2.img.xz | 2018-07-25 03:30 | 296M |
| ubuntu-18.04.1-preinstalled-server-armhf+raspi2.img.xz.zsync | 2018-07-26 16:49 | 519K |
| ubuntu-18.04.1-preinstalled-server-armhf+raspi2.manifest | 2018-07-25 03:30 | 13K |
| ubuntu-18.04.1-server-amd64.iso | 2018-07-25 03:00 | 715M |
| ubuntu-18.04.1-server-amd64.iso.torrent | 2018-07-26 16:52 | 28K |
| ubuntu-18.04.1-server-amd64.iso.zsync | 2018-07-26 16:52 | 1.4M |
| ubuntu-18.04.1-server-amd64.jigdo | 2018-07-26 16:52 | 134K |
| ubuntu-18.04.1-server-amd64.list | 2018-07-25 03:00 | 98K |
| ubuntu-18.04.1-server-amd64.manifest | 2018-07-25 02:53 | 5.4K |
| ubuntu-18.04.1-server-amd64.metalink | 2018-07-26 17:13 | 1.0K |
| ubuntu-18.04.1-server-amd64.template | 2018-07-25 03:00 | 131M |
| ubuntu-18.04.1-server-arm64.iso | 2018-07-25 03:02 | 672M |
| ubuntu-18.04.1-server-arm64.iso.torrent | 2018-07-26 16:53 | 26K |
| ubuntu-18.04.1-server-arm64.iso.zsync | 2018-07-26 16:53 | 1.3M |
| ubuntu-18.04.1-server-arm64.jigdo | 2018-07-26 16:53 | 159K |
| ubuntu-18.04.1-server-arm64.list | 2018-07-25 03:02 | 90K |
| ubuntu-18.04.1-server-arm64.manifest | 2018-07-25 02:58 | 5.4K |
| ubuntu-18.04.1-server-arm64.metalink | 2018-07-26 17:13 | 1.0K |
| ubuntu-18.04.1-server-arm64.template | 2018-07-25 03:02 | 79M |
| ubuntu-18.04.1-server-ppc64el.iso | 2018-07-25 03:03 | 739M |
| ubuntu-18.04.1-server-ppc64el.iso.torrent | 2018-07-26 16:53 | 29K |
| ubuntu-18.04.1-server-ppc64el.iso.zsync | 2018-07-26 16:53 | 1.4M |
| ubuntu-18.04.1-server-ppc64el.jigdo | 2018-07-26 16:53 | 164K |
| ubuntu-18.04.1-server-ppc64el.list | 2018-07-25 03:03 | 92K |
| ubuntu-18.04.1-server-ppc64el.manifest | 2018-07-25 02:55 | 5.7K |
| ubuntu-18.04.1-server-ppc64el.metalink | 2018-07-26 17:13 | 1.0K |
| ubuntu-18.04.1-server-ppc64el.template | 2018-07-25 03:03 | 90M |
| ubuntu-18.04.1-server-s390x.iso | 2018-07-25 03:04 | 567M |
| ubuntu-18.04.1-server-s390x.iso.torrent | 2018-07-26 16:53 | 22K |
| ubuntu-18.04.1-server-s390x.iso.zsync | 2018-07-26 16:53 | 1.1M |
| ubuntu-18.04.1-server-s390x.jigdo | 2018-07-26 16:53 | 126K |
| ubuntu-18.04.1-server-s390x.list | 2018-07-25 03:04 | 88K |
| ubuntu-18.04.1-server-s390x.manifest | 2018-07-25 02:53 | 5.4K |
| ubuntu-18.04.1-server-s390x.metalink | 2018-07-26 17:13 | 1.0K |
| ubuntu-18.04.1-server-s390x.template | 2018-07-25 03:04 | 115M |
| ubuntu-18.04.1.0-live-server-amd64.iso | 2018-11-29 22:30 | 812M |
| ubuntu-18.04.1.0-live-server-amd64.iso.torrent | 2018-11-29 23:27 | 32K |
| ubuntu-18.04.1.0-live-server-amd64.iso.zsync | 2018-11-29 23:27 | 1.6M |
| ubuntu-18.04.1.0-live-server-amd64.list | 2018-11-29 23:27 | 7.8K |
| ubuntu-18.04.1.0-live-server-amd64.manifest | 2018-11-29 23:27 | 14K |
| ubuntu-18.04.1.0-live-server-amd64.metalink | 2018-11-29 23:27 | 53K |
| ubuntu-18.04.2-desktop-amd64.iso | 2019-02-10 00:27 | 1.9G |
| ubuntu-18.04.2-desktop-amd64.iso.torrent | 2019-02-14 22:51 | 75K |
| ubuntu-18.04.2-desktop-amd64.iso.zsync | 2019-02-14 22:51 | 3.7M |
| ubuntu-18.04.2-desktop-amd64.list | 2019-02-10 00:27 | 7.8K |
| ubuntu-18.04.2-desktop-amd64.manifest | 2019-02-10 00:25 | 57K |
| ubuntu-18.04.2-desktop-amd64.metalink | 2019-02-14 22:53 | 47K |
| ubuntu-18.04.2-live-server-amd64.iso | 2019-02-14 10:06 | 834M |
| ubuntu-18.04.2-live-server-amd64.iso.torrent | 2019-02-14 22:53 | 33K |
| ubuntu-18.04.2-live-server-amd64.iso.zsync | 2019-02-14 22:53 | 1.6M |
| ubuntu-18.04.2-live-server-amd64.list | 2019-02-14 10:06 | 10K |
| ubuntu-18.04.2-live-server-amd64.manifest | 2019-02-14 10:04 | 14K |
| ubuntu-18.04.2-live-server-amd64.metalink | 2019-02-14 22:53 | 48K |
| ubuntu-18.04.2-preinstalled-server-arm64+raspi3.img.xz | 2019-02-10 00:51 | 419M |
| ubuntu-18.04.2-preinstalled-server-arm64+raspi3.img.xz.zsync | 2019-02-15 16:32 | 838K |
| ubuntu-18.04.2-preinstalled-server-arm64+raspi3.manifest | 2019-02-10 00:51 | 13K |
| ubuntu-18.04.2-preinstalled-server-armhf+raspi2.img.xz | 2019-02-10 00:52 | 302M |
| ubuntu-18.04.2-preinstalled-server-armhf+raspi2.img.xz.zsync | 2019-02-14 22:58 | 528K |
| ubuntu-18.04.2-preinstalled-server-armhf+raspi2.manifest | 2019-02-10 00:52 | 14K |
| ubuntu-18.04.2-preinstalled-server-armhf+raspi3.img.xz | 2019-02-10 00:48 | 419M |
| ubuntu-18.04.2-preinstalled-server-armhf+raspi3.img.xz.zsync | 2019-02-14 22:58 | 838K |
| ubuntu-18.04.2-preinstalled-server-armhf+raspi3.manifest | 2019-02-10 00:48 | 13K |
| ubuntu-18.04.2-server-amd64.iso | 2019-02-10 00:19 | 883M |
| ubuntu-18.04.2-server-amd64.iso.torrent | 2019-02-14 22:59 | 35K |
| ubuntu-18.04.2-server-amd64.iso.zsync | 2019-02-14 22:59 | 1.7M |
| ubuntu-18.04.2-server-amd64.jigdo | 2019-02-14 22:59 | 140K |
| ubuntu-18.04.2-server-amd64.list | 2019-02-10 00:19 | 103K |
| ubuntu-18.04.2-server-amd64.manifest | 2019-02-10 00:09 | 5.6K |
| ubuntu-18.04.2-server-amd64.metalink | 2019-02-14 23:00 | 1.0K |
| ubuntu-18.04.2-server-amd64.template | 2019-02-10 00:19 | 103M |
| ubuntu-18.04.2-server-arm64.iso | 2019-02-10 00:21 | 877M |
| ubuntu-18.04.2-server-arm64.iso.torrent | 2019-02-14 22:59 | 34K |
| ubuntu-18.04.2-server-arm64.iso.zsync | 2019-02-14 22:59 | 1.7M |
| ubuntu-18.04.2-server-arm64.jigdo | 2019-02-14 22:59 | 165K |
| ubuntu-18.04.2-server-arm64.list | 2019-02-10 00:21 | 94K |
| ubuntu-18.04.2-server-arm64.manifest | 2019-02-10 00:15 | 5.6K |
| ubuntu-18.04.2-server-arm64.metalink | 2019-02-14 23:00 | 1.0K |
| ubuntu-18.04.2-server-arm64.template | 2019-02-10 00:21 | 89M |
| ubuntu-18.04.2-server-ppc64el.iso | 2019-02-10 00:23 | 947M |
| ubuntu-18.04.2-server-ppc64el.iso.torrent | 2019-02-14 22:59 | 37K |
| ubuntu-18.04.2-server-ppc64el.iso.zsync | 2019-02-14 22:59 | 1.8M |
| ubuntu-18.04.2-server-ppc64el.jigdo | 2019-02-14 22:59 | 202K |
| ubuntu-18.04.2-server-ppc64el.list | 2019-02-10 00:23 | 96K |
| ubuntu-18.04.2-server-ppc64el.manifest | 2019-02-10 00:11 | 5.9K |
| ubuntu-18.04.2-server-ppc64el.metalink | 2019-02-14 23:00 | 1.0K |
| ubuntu-18.04.2-server-ppc64el.template | 2019-02-10 00:23 | 115M |
| ubuntu-18.04.2-server-s390x.iso | 2019-02-10 00:24 | 618M |
| ubuntu-18.04.2-server-s390x.iso.torrent | 2019-02-14 23:00 | 24K |
| ubuntu-18.04.2-server-s390x.iso.zsync | 2019-02-14 23:00 | 1.2M |
| ubuntu-18.04.2-server-s390x.jigdo | 2019-02-14 22:59 | 129K |
| ubuntu-18.04.2-server-s390x.list | 2019-02-10 00:24 | 92K |
| ubuntu-18.04.2-server-s390x.manifest | 2019-02-10 00:09 | 5.6K |
| ubuntu-18.04.2-server-s390x.metalink | 2019-02-14 23:00 | 1.0K |
| ubuntu-18.04.2-server-s390x.template | 2019-02-10 00:24 | 133M |
| ubuntu-18.04.3-desktop-amd64.iso | 2019-08-05 19:29 | 1.9G |
| ubuntu-18.04.3-desktop-amd64.iso.torrent | 2019-08-08 12:16 | 78K |
| ubuntu-18.04.3-desktop-amd64.iso.zsync | 2019-08-08 12:16 | 3.9M |
| ubuntu-18.04.3-desktop-amd64.list | 2019-08-05 19:29 | 7.8K |
| ubuntu-18.04.3-desktop-amd64.manifest | 2019-08-05 19:26 | 58K |
| ubuntu-18.04.3-desktop-amd64.metalink | 2020-02-12 13:42 | 48K |
| ubuntu-18.04.3-live-server-amd64.iso | 2019-08-05 20:00 | 848M |
| ubuntu-18.04.3-live-server-amd64.iso.torrent | 2019-08-08 12:19 | 33K |
| ubuntu-18.04.3-live-server-amd64.iso.zsync | 2019-08-08 12:19 | 1.7M |
| ubuntu-18.04.3-live-server-amd64.list | 2019-08-05 20:00 | 10K |
| ubuntu-18.04.3-live-server-amd64.manifest | 2019-08-05 19:34 | 14K |
| ubuntu-18.04.3-live-server-amd64.metalink | 2020-02-12 13:42 | 50K |
| ubuntu-18.04.3-preinstalled-server-arm64+raspi3.img.xz | 2019-08-05 19:14 | 441M |
| ubuntu-18.04.3-preinstalled-server-arm64+raspi3.img.xz.zsync | 2019-08-08 12:41 | 882K |
| ubuntu-18.04.3-preinstalled-server-arm64+raspi3.manifest | 2019-08-05 19:14 | 14K |
| ubuntu-18.04.3-preinstalled-server-armhf+raspi2.img.xz | 2019-08-05 19:19 | 312M |
| ubuntu-18.04.3-preinstalled-server-armhf+raspi2.img.xz.zsync | 2019-08-08 12:41 | 546K |
| ubuntu-18.04.3-preinstalled-server-armhf+raspi2.manifest | 2019-08-05 19:19 | 15K |
| ubuntu-18.04.3-preinstalled-server-armhf+raspi3.img.xz | 2019-08-05 19:10 | 440M |
| ubuntu-18.04.3-preinstalled-server-armhf+raspi3.img.xz.zsync | 2019-08-08 12:41 | 881K |
| ubuntu-18.04.3-preinstalled-server-armhf+raspi3.manifest | 2019-08-05 19:10 | 14K |
| ubuntu-18.04.3-server-amd64.iso | 2019-08-05 18:43 | 900M |
| ubuntu-18.04.3-server-amd64.iso.torrent | 2019-08-08 12:42 | 35K |
| ubuntu-18.04.3-server-amd64.iso.zsync | 2019-08-08 12:42 | 1.8M |
| ubuntu-18.04.3-server-amd64.jigdo | 2019-08-08 12:42 | 141K |
| ubuntu-18.04.3-server-amd64.list | 2019-08-05 18:43 | 103K |
| ubuntu-18.04.3-server-amd64.manifest | 2019-08-05 18:32 | 5.8K |
| ubuntu-18.04.3-server-amd64.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.3-server-amd64.template | 2019-08-05 18:43 | 104M |
| ubuntu-18.04.3-server-arm64.iso | 2019-08-05 18:45 | 903M |
| ubuntu-18.04.3-server-arm64.iso.torrent | 2019-08-08 12:42 | 35K |
| ubuntu-18.04.3-server-arm64.iso.zsync | 2019-08-08 12:42 | 1.8M |
| ubuntu-18.04.3-server-arm64.jigdo | 2019-08-08 12:42 | 165K |
| ubuntu-18.04.3-server-arm64.list | 2019-08-05 18:45 | 95K |
| ubuntu-18.04.3-server-arm64.manifest | 2019-08-05 18:40 | 5.8K |
| ubuntu-18.04.3-server-arm64.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.3-server-arm64.template | 2019-08-05 18:45 | 90M |
| ubuntu-18.04.3-server-ppc64el.iso | 2019-08-05 18:47 | 968M |
| ubuntu-18.04.3-server-ppc64el.iso.torrent | 2019-08-08 12:43 | 38K |
| ubuntu-18.04.3-server-ppc64el.iso.zsync | 2019-08-08 12:43 | 1.9M |
| ubuntu-18.04.3-server-ppc64el.jigdo | 2019-08-08 12:43 | 203K |
| ubuntu-18.04.3-server-ppc64el.list | 2019-08-05 18:47 | 97K |
| ubuntu-18.04.3-server-ppc64el.manifest | 2019-08-05 18:35 | 6.1K |
| ubuntu-18.04.3-server-ppc64el.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.3-server-ppc64el.template | 2019-08-05 18:47 | 117M |
| ubuntu-18.04.3-server-s390x.iso | 2019-08-05 18:49 | 627M |
| ubuntu-18.04.3-server-s390x.iso.torrent | 2019-08-08 12:43 | 25K |
| ubuntu-18.04.3-server-s390x.iso.zsync | 2019-08-08 12:43 | 1.2M |
| ubuntu-18.04.3-server-s390x.jigdo | 2019-08-08 12:43 | 130K |
| ubuntu-18.04.3-server-s390x.list | 2019-08-05 18:49 | 92K |
| ubuntu-18.04.3-server-s390x.manifest | 2019-08-05 18:34 | 5.8K |
| ubuntu-18.04.3-server-s390x.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.3-server-s390x.template | 2019-08-05 18:49 | 134M |
| ubuntu-18.04.4-desktop-amd64.iso | 2020-02-03 18:40 | 2.0G |
| ubuntu-18.04.4-desktop-amd64.iso.torrent | 2020-02-12 13:41 | 80K |
| ubuntu-18.04.4-desktop-amd64.iso.zsync | 2020-02-12 13:41 | 4.0M |
| ubuntu-18.04.4-desktop-amd64.list | 2020-02-03 18:40 | 7.8K |
| ubuntu-18.04.4-desktop-amd64.manifest | 2020-02-03 18:37 | 59K |
| ubuntu-18.04.4-desktop-amd64.metalink | 2020-02-12 13:42 | 48K |
| ubuntu-18.04.4-live-server-amd64.iso | 2020-02-03 18:36 | 870M |
| ubuntu-18.04.4-live-server-amd64.iso.torrent | 2020-02-12 13:40 | 34K |
| ubuntu-18.04.4-live-server-amd64.iso.zsync | 2020-02-12 13:40 | 1.7M |
| ubuntu-18.04.4-live-server-amd64.list | 2020-02-03 18:36 | 10K |
| ubuntu-18.04.4-live-server-amd64.manifest | 2020-02-03 18:34 | 14K |
| ubuntu-18.04.4-live-server-amd64.metalink | 2020-02-12 13:42 | 50K |
| ubuntu-18.04.4-preinstalled-server-arm64+raspi3.img.xz | 2020-02-03 18:43 | 477M |
| ubuntu-18.04.4-preinstalled-server-arm64+raspi3.img.xz.zsync | 2020-02-12 13:37 | 954K |
| ubuntu-18.04.4-preinstalled-server-arm64+raspi3.manifest | 2020-02-03 18:43 | 14K |
| ubuntu-18.04.4-preinstalled-server-arm64+raspi4.img.xz | 2020-02-03 18:43 | 477M |
| ubuntu-18.04.4-preinstalled-server-arm64+raspi4.img.xz.zsync | 2020-02-12 13:37 | 954K |
| ubuntu-18.04.4-preinstalled-server-arm64+raspi4.manifest | 2020-02-03 18:43 | 14K |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi2.img.xz | 2020-02-03 18:40 | 472M |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi2.img.xz.zsync | 2020-02-12 13:38 | 943K |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi2.manifest | 2020-02-03 18:40 | 14K |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi3.img.xz | 2020-02-03 18:40 | 472M |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi3.img.xz.zsync | 2020-02-12 13:38 | 943K |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi3.manifest | 2020-02-03 18:40 | 14K |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi4.img.xz | 2020-02-03 18:40 | 472M |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi4.img.xz.zsync | 2020-02-12 13:38 | 943K |
| ubuntu-18.04.4-preinstalled-server-armhf+raspi4.manifest | 2020-02-03 18:40 | 14K |
| ubuntu-18.04.4-server-amd64.iso | 2020-02-03 18:33 | 921M |
| ubuntu-18.04.4-server-amd64.iso.torrent | 2020-02-12 13:38 | 36K |
| ubuntu-18.04.4-server-amd64.iso.zsync | 2020-02-12 13:38 | 1.8M |
| ubuntu-18.04.4-server-amd64.jigdo | 2020-02-12 13:38 | 141K |
| ubuntu-18.04.4-server-amd64.list | 2020-02-03 18:33 | 104K |
| ubuntu-18.04.4-server-amd64.manifest | 2020-02-03 18:26 | 5.8K |
| ubuntu-18.04.4-server-amd64.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.4-server-amd64.template | 2020-02-03 18:33 | 105M |
| ubuntu-18.04.4-server-arm64.iso | 2020-02-03 18:35 | 953M |
| ubuntu-18.04.4-server-arm64.iso.torrent | 2020-02-12 13:38 | 37K |
| ubuntu-18.04.4-server-arm64.iso.zsync | 2020-02-12 13:38 | 1.9M |
| ubuntu-18.04.4-server-arm64.jigdo | 2020-02-12 13:38 | 170K |
| ubuntu-18.04.4-server-arm64.list | 2020-02-03 18:35 | 98K |
| ubuntu-18.04.4-server-arm64.manifest | 2020-02-03 18:29 | 5.8K |
| ubuntu-18.04.4-server-arm64.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.4-server-arm64.template | 2020-02-03 18:35 | 91M |
| ubuntu-18.04.4-server-ppc64el.iso | 2020-02-03 18:37 | 1.0G |
| ubuntu-18.04.4-server-ppc64el.iso.torrent | 2020-02-12 13:39 | 39K |
| ubuntu-18.04.4-server-ppc64el.iso.zsync | 2020-02-12 13:39 | 1.9M |
| ubuntu-18.04.4-server-ppc64el.jigdo | 2020-02-12 13:38 | 204K |
| ubuntu-18.04.4-server-ppc64el.list | 2020-02-03 18:37 | 97K |
| ubuntu-18.04.4-server-ppc64el.manifest | 2020-02-03 18:28 | 6.1K |
| ubuntu-18.04.4-server-ppc64el.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.4-server-ppc64el.template | 2020-02-03 18:37 | 118M |
| ubuntu-18.04.4-server-s390x.iso | 2020-02-03 18:38 | 638M |
| ubuntu-18.04.4-server-s390x.iso.torrent | 2020-02-12 13:39 | 25K |
| ubuntu-18.04.4-server-s390x.iso.zsync | 2020-02-12 13:39 | 1.2M |
| ubuntu-18.04.4-server-s390x.jigdo | 2020-02-12 13:39 | 130K |
| ubuntu-18.04.4-server-s390x.list | 2020-02-03 18:38 | 93K |
| ubuntu-18.04.4-server-s390x.manifest | 2020-02-03 18:26 | 5.8K |
| ubuntu-18.04.4-server-s390x.metalink | 2020-02-12 14:10 | 1.0K |
| ubuntu-18.04.4-server-s390x.template | 2020-02-03 18:38 | 135M |
Tutorial
A previous version of this tutorial was written by Hazel Virdó
Introduction
UFW, or Uncomplicated Firewall, is an interface to iptables that is geared towards simplifying the process of configuring a firewall. While iptables is a solid and flexible tool, it can be difficult for beginners to learn how to use it to properly configure a firewall. If you're looking to get started securing your network, and you're not sure which tool to use, UFW may be the right choice for you.
This tutorial will show you how to set up a firewall with UFW on Ubuntu 18.04.
Prerequisites
To follow this tutorial, you will need:
- One Ubuntu 18.04 server with a sudo non-root user, which you can set up by following Steps 1–3 in the Initial Server Setup with Ubuntu 18.04 tutorial.
UFW is installed by default on Ubuntu. Open source office suite for mac. If it has been uninstalled for some reason, you can install it with sudo apt install ufw.
Step 1 — Using IPv6 with UFW (Optional)
This tutorial is written with IPv4 in mind, but will work for IPv6 as well as long as you enable it. If your Ubuntu server has IPv6 enabled, ensure that UFW is configured to support IPv6 so that it will manage firewall rules for IPv6 in addition to IPv4. To do this, open the UFW configuration with nano or your favorite editor.
Then make sure the value of IPV6 is yes. It should look like this:
Save and close the file. Now, when UFW is enabled, it will be configured to write both IPv4 and IPv6 firewall rules. However, before enabling UFW, we will want to ensure that your firewall is configured to allow you to connect via SSH. Let's start with setting the default policies.
Step 2 — Setting Up Default Policies
If you're just getting started with your firewall, the first rules to define are your default policies. These rules control how to handle traffic that does not explicitly match any other rules. By default, UFW is set to deny all incoming connections and allow all outgoing connections. This means anyone trying to reach your server would not be able to connect, while any application within the server would be able to reach the outside world.
Let's set your UFW rules back to the defaults so we can be sure that you'll be able to follow along with this tutorial. To set the defaults used by UFW, use these commands:
These commands set the defaults to deny incoming and allow outgoing connections. These firewall defaults alone might suffice for a personal computer, but servers typically need to respond to incoming requests from outside users. We'll look into that next.
Step 3 — Allowing SSH Connections
If we enabled our UFW firewall now, it would deny all incoming connections. This means that we will need to create rules that explicitly allow legitimate incoming connections — SSH or HTTP connections, for example — if we want our server to respond to those types of requests. If you're using a cloud server, you will probably want to allow incoming SSH connections so you can connect to and manage your server.
To configure your server to allow incoming SSH connections, you can use this command:
This will create firewall rules that will allow all connections on port 22, which is the port that the SSH daemon listens on by default. UFW knows what port allow ssh means because it's listed as a service in the /etc/services file.
However, we can actually write the equivalent rule by specifying the port instead of the service name. For example, this command works the same as the one above:
If you configured your SSH daemon to use a different port, you will have to specify the appropriate port. For example, if your SSH server is listening on port 2222, you can use this command to allow connections on that port:
Now that your firewall is configured to allow incoming SSH connections, we can enable it.
Step 4 — Enabling UFW
To enable UFW, use this command:
You will receive a warning that says the command may disrupt existing SSH connections. Fnaf piano notes easy. We already set up a firewall rule that allows SSH connections, so it should be fine to continue. Respond to the prompt with y and hit ENTER.
The firewall is now active. Ubuntu 19 4. Run the sudo ufw status verbose command to see the rules that are set. The rest of this tutorial covers how to use UFW in more detail, like allowing or denying different kinds of connections.
Step 5 — Allowing Other Connections
At this point, you should allow all of the other connections that your server needs to respond to. The connections that you should allow depends on your specific needs. Luckily, you already know how to write rules that allow connections based on a service name or port; we already did this for SSH on port 22. You can also do this for:
- HTTP on port 80, which is what unencrypted web servers use, using
sudo ufw allow httporsudo ufw allow 80 - HTTPS on port 443, which is what encrypted web servers use, using
sudo ufw allow httpsorsudo ufw allow 443
There are several others ways to allow other connections, aside from specifying a port or known service.
Specific Port Ranges
You can specify port ranges with UFW. Some applications use multiple ports, instead of a single port.
For example, to allow X11 connections, which use ports 6000-6007, use these commands:
When specifying port ranges with UFW, you must specify the protocol (tcp or udp) that the rules should apply to. We haven't mentioned this before because not specifying the protocol automatically allows both protocols, which is OK in most cases.
Specific IP Addresses
When working with UFW, you can also specify IP addresses. For example, if you want to allow connections from a specific IP address, such as a work or home IP address of 203.0.113.4, you need to specify from, then the IP address:
You can also specify a specific port that the IP address is allowed to connect to by adding to any port followed by the port number. For example, If you want to allow 203.0.113.4 to connect to port 22 (SSH), use this command:
Subnets
If you want to allow a subnet of IP addresses, you can do so using CIDR notation to specify a netmask. For example, if you want to allow all of the IP addresses ranging from 203.0.113.1 to 203.0.113.254 you could use this command:
Likewise, you may also specify the destination port that the subnet 203.0.113.0/24 is allowed to connect to. Again, we'll use port 22 (SSH) as an example:
Connections to a Specific Network Interface
If you want to create a firewall rule that only applies to a specific network interface, you can do so by specifying 'allow in on' followed by the name of the network interface.
You may want to look up your network interfaces before continuing. To do so, use this command:
The highlighted output indicates the network interface names. They are typically named something like eth0 or enp3s2.
So, if your server has a public network interface called eth0, you could allow HTTP traffic (port 80) to it with this command:
Doing so would allow your server to receive HTTP requests from the public internet.
Or, if you want your MySQL database server (port 3306) to listen for connections on the private network interface eth1, for example, you could use this command:
This would allow other servers on your private network to connect to your MySQL database.
Step 6 — Denying Connections
If you haven't changed the default policy for incoming connections, UFW is configured to deny all incoming connections. Generally, this simplifies the process of creating a secure firewall policy by requiring you to create rules that explicitly allow specific ports and IP addresses through.
However, sometimes you will want to deny specific connections based on the source IP address or subnet, perhaps because you know that your server is being attacked from there. Also, if you want to change your default incoming policy to allow (which is not recommended), you would need to create deny rules for any services or IP addresses that you don't want to allow connections for.
To write deny rules, you can use the commands described above, replacing allow with deny.
For example, to deny HTTP connections, you could use this command:
Or if you want to deny all connections from 203.0.113.4 you could use this command:
Now let's take a look at how to delete rules.
Step 7 — Deleting Rules
Knowing how to delete firewall rules is just as important as knowing how to create them. There are two different ways to specify which rules to delete: by rule number or by the actual rule (similar to how the rules were specified when they were created). We'll start with the delete by rule number method because it is easier.
By Rule Number
If you're using the rule number to delete firewall rules, the first thing you'll want to do is get a list of your firewall rules. The UFW status command has an option to display numbers next to each rule, as demonstrated here:
If we decide that we want to delete rule 2, the one that allows port 80 (HTTP) connections, we can specify it in a UFW delete command like this:
This would show a confirmation prompt then delete rule 2, which allows HTTP connections. Note that if you have IPv6 enabled, you would want to delete the corresponding IPv6 rule as well.
By Actual Rule
The alternative to rule numbers is to specify the actual rule to delete. For example, if you want to remove the allow http rule, you could write it like this: Bookends 12 6 1 download free.
You could also specify the rule by allow 80, instead of by service name:
This method will delete both IPv4 and IPv6 rules, if they exist.
Step 8 — Checking UFW Status and Rules
The alternative to rule numbers is to specify the actual rule to delete. For example, if you want to remove the allow http rule, you could write it like this: Bookends 12 6 1 download free.
You could also specify the rule by allow 80, instead of by service name:
This method will delete both IPv4 and IPv6 rules, if they exist.
Step 8 — Checking UFW Status and Rules
At any time, you can check the status of UFW with this command:
If UFW is disabled, which it is by default, you'll see something like this:
Ubuntu Server 18 04
If UFW is active, which it should be if you followed Step 3, the output will say that it's active and it will list any rules that are set. For example, if the firewall is set to allow SSH (port 22) connections from anywhere, the output might look something like this:
Use the status command if you want to check how UFW has configured the firewall.
Step 9 — Disabling or Resetting UFW (optional)
If you decide you don't want to use UFW, you can disable it with this command:
Any rules that you created with UFW will no longer be active. You can always run sudo ufw enable if you need to activate it later.
18.04 Ubuntu Download
If you already have UFW rules configured but you decide that you want to start over, you can use the reset command:
Install Ubuntu 18 04
This will disable UFW and delete any rules that were previously defined. Keep in mind that the default policies won't change to their original settings, if you modified them at any point. This should give you a fresh start with UFW.
Conclusion
Your firewall is now configured to allow (at least) SSH connections. Be sure to allow any other incoming connections that your server requires, while limiting any unnecessary connections, so your server will be functional and secure.
To learn about more common UFW configurations, check out the UFW Essentials: Common Firewall Rules and Commands tutorial.
